Antivirus is a staple security solution for businesses and everyday PC users, but have you ever considered how it works? By thinking through some of the details, you might gain a greater understanding of how antivirus works, what it does, and why you need to keep it updated. Today, we’re going to discuss just that, starting from square one.
Datalyst Blog
We will always reinforce how critical it is for everyone in any workplace to have a grasp of cybersecurity best practices, regardless of their role or responsibilities. However, based on a survey conducted by UK-based cybersecurity firm Ramsac, this baseline is not being met by a long shot.
Why do we say this? Simple: this survey revealed that one in three adults failed a cybersecurity test designed for 11-year-olds.
Absolutely nobody likes dealing with passwords. They’re annoying, hard to remember, and yet, somehow, hackers seem to have no problem cracking them. That’s where password managers come in. They take the stress out of remembering a hundred different logins while keeping your business secure. If you’re still relying on sticky notes or using the same password for everything so you can remember it, it’s time to make the switch.
You don’t want to get spammed; nobody does. Unfortunately, it happens to EVERYONE, and it’s just getting worse. All this unwelcome correspondence happens over the phone, through email, and especially on social media. In today’s blog, we’ll talk a little bit about how social media puts users at risk and what you can do to keep that risk from becoming a problem for you.
With remote work remaining popular, employees can benefit from flexibility and work-life balance, but at the cost of certain challenges on the business side. The big one is security, as your network ends up spread out across multiple locations rather than siloed in-house. Here are three rules you should consider when planning out how to approach remote work.
Think about the apps you use daily—Google Drive, Netflix, Spotify, even Instagram. All of these run on cloud-based services, which basically means they store and process everything online instead of relying on one physical device. Businesses, big and small, are making the same shift because, honestly, it just makes sense. Let’s take a look at why you should be looking to use cloud services in your business.
Text messages are great. They’re a quick and effective means for us all to communicate.
Unfortunately, this does bring some downsides, too… namely, they’re a relatively simple means for a scammer to spread their attacks. Let’s discuss why this is so dangerous and how you can identify and avoid these threats.
The Internet is a fantastic place to shop, connect, and learn, but people also have to deal with the minefield of scams—especially in 2025, where opportunists are getting even craftier with AI and other high-tech tricks. This month, we take a look at four simple ways you can spot an Internet scam before it drains your wallet or your personal data.
It’s undeniable that the smartphone has transformed computing. In fact, not only is more computing done on mobile devices, they are by far the most purchased computers in the world. Well over 90 percent of people own some type of smartphone. So how do you use these devices for productivity? This month, we will discuss some ways to make this happen.
Mobile device security is critical for modern businesses, especially as they play a more prominent and significant role in daily operations. However, data loss is also a problem, regardless of the source… including if a device is wiped via a reset.
While Apple has offered a feature to prevent this for the past year or so, Android 15 now provides the same, referred to as Identity Check. Let’s explore how it works, and how to enable it for yourself.
When hackers steal data, they don't just sit on it. Sometimes they delete it, but most of the time, they sell it or use it for illegal activities. A lot of this stolen data ends up on the Dark Web, a hidden part of the Internet where people do shady things. That's why it's so important to keep an eye on the Dark Web to protect your business.
Have you ever suspected that a hacker could silently observe your email interactions with your clients and your staff? If you manage your own email infrastructure, we want to highlight the importance of email encryption. Encryption keeps your business’ email communications secure and compliant so you can worry less about security and privacy to focus more on running your business.
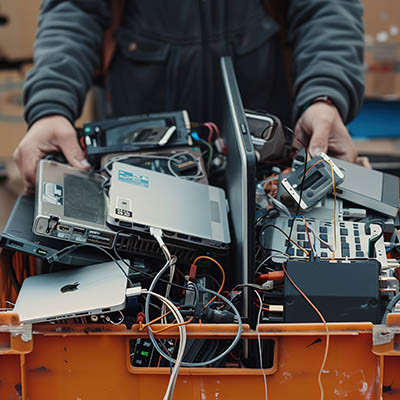
So you got a new computer for a holiday gift. That’s great! We’re excited that you’re excited. But you also need to consider how you are going to dispose of your old device and how to do so in a safe way. Today, we want to discuss how you can safely discard, or potentially even reuse, your old device so you don’t put your data at risk.
Most people are familiar with Santa Claus, the jolly gift-giver who delivers presents to all the children who have kept the Christmas spirit in their hearts all year. Lately, many people have also become aware of Krampus, Santa’s dark shadow who—as the legend goes—takes a similar trip to visit the naughty children and turn the worst into a midnight snack.
However, one has to wonder: what about all the adults who might also be naughty?